Do more with emaus
Our Strategy
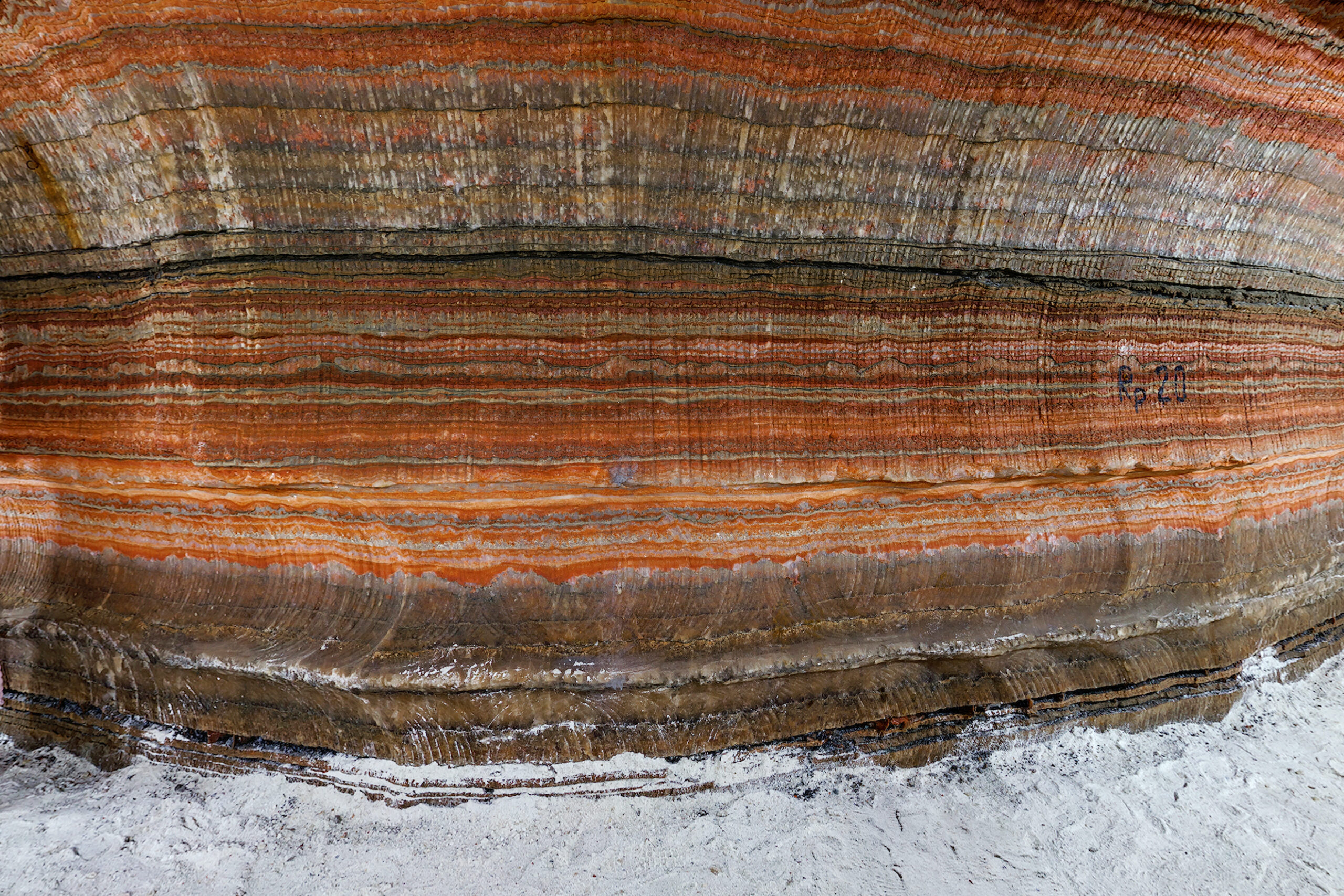
To address this complex challenge, we designed a multifaceted cybersecurity defense mechanism. It involved deploying an advanced anomaly detection system capable of identifying even the most discreet signs of network compromise. Simultaneously, we engaged in a thorough examination of historical cyber-attack patterns, specifically those that targeted the natural resources sector, to anticipate potential subsequent moves by the attackers.